About Us
JSmith Cyber Blog is a cybersecurity blog built to inform, explain, and protect. We cover real threats, break down complex topics, and give you clear, practical insight into the digital world one post at a time.
Founded by Jeremy, a passionate cybersecurity researcher and writer, this blog is a space for people who care about online safety, privacy, and understanding how the internet really works.
What We Do
We publish
- Real-world cybersecurity news and analysis
- Breakdowns of hacks, breaches, and vulnerabilities
- Privacy tips and tools for everyday users
- Guides to help you stay secure whether you’re tech savvy
- Expert opinions and community stories

Why This Blog Exists
Cybersecurity affects everyone, but most people only hear about it when something goes wrong. We believe that education, clarity, and awareness can change that. Whether it’s a new phishing scam or a major data leak, we’re here to explain what happened, why it matters, and how to protect yourself.
Who We’re For

- IT professionals looking for real updates
- Curious readers trying to stay safe online
- Small business owners managing digital risks
- Students and learners interested in security
- Anyone who wants a no-BS take on what’s happening in cybersecur
I started this blog because I got tired of vague headlines, overhyped threats, and recycled info. I wanted a place where we could talk about what’s really happening clearly, honestly, and in plain language. If that’s what you’re looking for, welcome
Create your first networking automation tool with bash
I used to think scripting was only for programmers (of which I am not) but AI has been a game changer – at least for me. today I want to share my first ip sweeper bash script, my process and some of the insights I gained a long the way.
An Ip Sweeper is a great network scanning tool to do a quick check of currently active systems on your network. This is an important reconnaissance step for an ethical hacker or pen tester. There are many network featers and tools available to advance this project beyond just scanning for active ips but let’s leave that for another day.
Preliminary
The following are the logical steps to think through and tasks followed to build this Ip Sweeper
Identify your network sub-net
- ip a → this command will show the interfaces on your nic. From this information you should be able to identify what your sub-net and ip are.

Test ping an ip in the sub-net
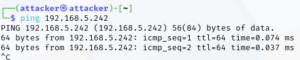
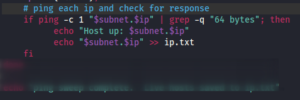
Set the ping count to 1 and send the output to text file. To grab the line pertaining the ip, we can pipe “|” grep the standard “64 bytes” message from the file to return the ping output to the terminal.
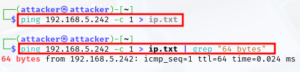
We only want to return the ip address so we can pipe that to the cut command and add a delimiter so only the ip is returned. The delimiter specified is a space and (-f 4) # of spaces to count before displaying output.
![]()
Then one last pipe to use the translate utility to remove the colon from the already delimited output.
![]()
Now this string of piped commands can be used to build our script!
Now we are ready to structure the piped commands into a series of loops and statements. The intent is to create a network automation tool, useful for troubleshooting and reconnaissance.
Procedure
Create .sh file – I use mouse-pad but use what you prefer.
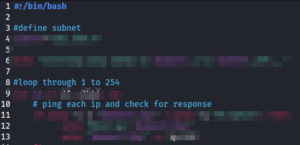
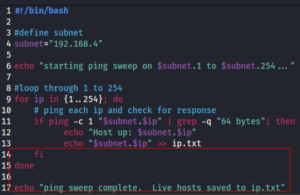
![]()
A bash script always starts with → #!/bin/bash or “shbang” → The shbang declares what scripting shell is being used.
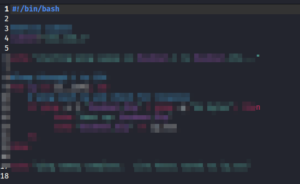
Now to determine the logic → using comments to define the flow statements. Comments are portions of the script that are non executable and are used to describe the different actions taken. A comment is created by first using the # sign. This tells program to ignore the line as part of the script.
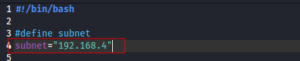
Now for the logic, first we set a variable to represent the subnet of our network
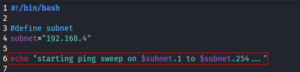
An echo statement is used to print every ip instance found when the script runs and pass arguments to the script. We must identify the range with in the variable to be searched. adding the $ in front of the variable to pass the argument.
Next we use the for statement to set the parameter for the action to be performed → search all ips in the subnet range defined by the ip variable.
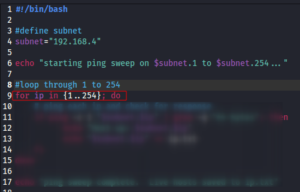
Next step is the if, then statement → we use the piped commands from before to build the if, then statement → Only changes: replaced 192.168.5 with two arguments → $subnet and $ip “$subnet.$ip”, 192.168.5 = $subnet and .x (last octet of ip) = $.ip → This paramenter was initially defined in the “starting ping sweep” echo statement above. The then statement that follows below, prints to terminal each host that is ping-able (up) and prints line output as input to ip.txt.
Next is the close the for, if, then loop with fi and done. I added an additional echo statement to indicate when the ip sweep is complete.
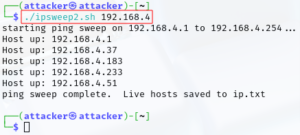
This completes the script. Below is example output of the script running successfully. For executing this script we can use the following arguments
./ , filename, and the first 3 octets of the ip range so:
./ipsweep2.sh 192.168.4
Below we see 5 ips were identified on the /24 sub-net.
Conclusion
In conclusion, this exercise was relatively straight forward. With the help of AI, a little bit of networking knowledge and some knowledge of how loops and operators work; anyone can automate a network troubleshooting step like this!
